As organizations worldwide settle into their respective hybrid working game-plans, the unfamiliar is becoming the accepted.
A work culture that seemed impossible, or at least unlikely before the pandemic, is now the sanctioned way of doing things, and moving forward, this new culture will continue to evolve.
Part of this evolution is the usage of personal ‘Bring Your Own Devices’ – or BYOD. In fact, a study by Bitglass revealed that at least 82% of organizations have actively enabled BYOD to some extent.
In this blog, we’ll address some of the benefits and pitfalls of BYOD in the workplace, and how to manage a BYOD architecture.
Let’s face it – without the use of personal devices during the pandemic, businesses simply couldn’t have continued to operate. On the other hand, the hybrid work model has not only created complexity, but expedited security concerns and challenges around the use of personal devices.
The benefits of BYOD
The reduction of content sprawl and increased resilience in the post-pandemic workplace are the overall benefits of BYOD, according to research from Gartner. The consensus is that enabling employees to use their own devices can lead to more personal satisfaction and productivity, due to greater flexibility and mobility.
Further insights in a study by Samsung revealed that:
- 82% of employees agree that using their own mobile devices is mission-critical to work ethic, and increases productivity and decision-making.
- 76% said mobile devices have a positive impact on customer service and satisfaction.
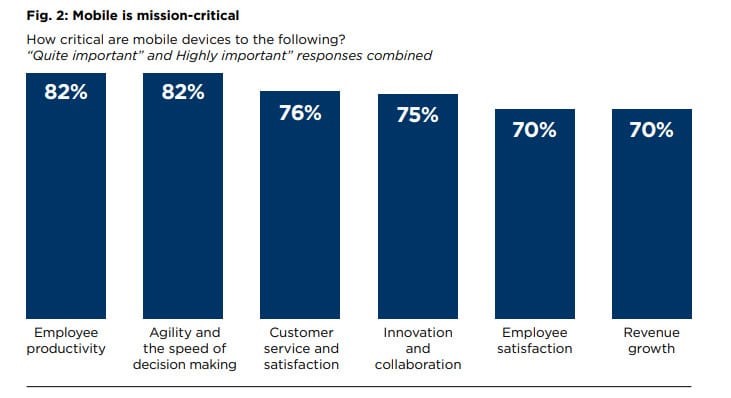
Image source: Comparitech
Other benefits include:
- A reduction in device management for business-owned devices
- Decreased spending on hardware and software licensing
- More devices for users to choose from, creating added efficiency
- Greater trust in leadership
BYOD management challenges
The pandemic opened a Pandora’s Box for IT management in terms of security and visibility with the increased adoption of unmanaged Software-as-a-Service (SaaS) solutions and the use of personal, non-corporate issued devices.
Effectively securing an organization’s resources and data means making BYOD user and device identity and access management the primary security focus.

Image source: Simplilearn
Device trust and management is crucial
Controlling the risks of unmanaged devices is not a new concept, it’s simply becoming more prevalent and important, with the adoption of hybrid working. Organizations need to ensure that all their active devices can be properly identified and given the appropriate access level.
From desktops and notebooks to personal tablets, mobile phones and QA machines used by developers, it’s crucial to accurately identify all the devices used by employees.
Zero Trust policies (the strategic approach to cybersecurity that eliminates implicit trust and continuously validates every digital interaction) need to be consistently enforced and devices continuously monitored.
Ensuring user and device identity
Once device trust is established, it’s important to identify which devices are managed by the organization, and ensure they are properly postured and updated so that they can be allocated high levels of security clearance.
This is vital in a cloud-centric world where employees can access applications from any device and from any location.
Monitoring has never been more important
Businesswire predicts the global mobile device management market size to grow from USD 5.5 Billion in 2021 to USD 20.4 Billion by 2026, at a Compound Annual Growth Rate (CAGR) of 29.8% during the forecast period.
This highlights the importance of providing a streamlined and secure network device management strategy - as a MSP provider as well as an IT service manager.
Before deploying multiple device strategies, organizations need to consider BYOD management initiatives regarding remote device management.
The ultimate goal for any enterprise, particularly in a hybrid working ecosystem, is staying connected, productive, and secure. BYOD policies are making this a reality, but it’s vital to be able to see inside your entire unified communications ecosystem and to have the ability to monitor and manage every device, end user and location. You need to be able to pinpoint vulnerabilities and pre-empt security risks.
Read our comprehensive guide
Hybrid Workplace Models are the New Normal
How IR Collaborate can support your BYOD strategies
With IR Collaborate, IT teams can track exactly which apps and devices are being used by which employee, their locations, and even data usage. Full visibility and endpoint accountability can even enable teams to prevent problems before they happen, which is invaluable for the end user.
Whether employees are on-premises using corporate supplied devices, or working primarily with BYO devices, or a combination of both, device monitoring and management is a critical part of securing applications and data, and enabling business continuity – and success.


.png?width=141&height=141&name=Transact%20(1).png)











